Oh 702 requires a warrant already for the actual collection, alright. And it's a generalized warrant, it's not a specific right. We go through the court to review the bidding, alright. 702 is a reflection of the telecommunications reality that there are a whole bunch of communications. We talk about digital communications, right? 702 allows the NSA to force and Facebook and other companies to provide information of other costs about specific accounts, right? Sure, right. And in the upstream portion of it, action allows NSA to collect it, right? Like true electronic surveillance. So you've got, so let's me can get it at rest, you can get it at motion, both authorized by revision of the FISA Act section 702. Are the rules too broad, though? Do they allow the FBI or other agencies don't accident? So NSA's allowed to either collect or ask passive or active endpoint or in transit on legitimate intelligence targets that they have reason to believe are not US persons and are outside the United States. That's vanilla, that's what NSA does all the time, alright? And then it collects all that stuff, that's good, sure. It is based on the reality that not all the emails in America are of America, but not all the emails transiting America are of Americans. And we take advantage of what our realities with regard to global comms pass. Now what you're asking is deserve your, okay? You're not challenging the collection, right? You are asking about what then happens after the collection and what happens now is that agencies beyond NSA are allowed to query, listen to my words carefully because it really matters, are allowed to query what is unarguably legitimately collected foreign intelligence, this big stack of stuff. To query that stack with what...
Award-winning PDF software





Counterintelligence as defined in executive order 12333 as amended is ination Form: What You Should Know
U.S. Intelligence Activities: Authorized Intelligence Activities. 1. Purpose The purposes of this order are to establish procedures and guidelines for the intelligence activities of the intelligence community regarding the United States Government, to protect the privacy and civil liberties of persons engaged in, or who may be involved in, intelligence activities for, or on behalf of, the United States Government; 2. Definitions The following definitions shall apply throughout this order. (c) ``Affiliated entity'' means an entity that is a member of the community of intelligence services; has entered into intelligence cooperation agreement with an affiliate entity under this order, and that has an interest in operating intelligence activities with and on behalf of another entity under this order; 3. Prohibition.--It is prohibited except as provided in section 4 of this order, information or an intelligence activity that is directly or indirectly collateral to the counterintelligence interests of the United States or of any other Country shall be disseminated or otherwise used (1) to the public, (2) to any person in any manner, to any news media or commercial advertising agency in any country, and (3) for the purposes of communications intelligence, to-- (i) foreign governments or foreign organizations as defined in section 3.5 of this order; (ii) any other person that is not in the United States at the time when the information or intelligence activity is acquired; and (iii) any person or entity within the United States; 4. Protections. (a) Protections for United States persons.--This order shall not be interpreted or applied, unless consistent with all relevant safeguards against unlawful discrimination under the law, or unless necessary to protect the national security of the United States. In particular, no person within the United States shall be subjected to any infringement of the rights set forth in this order. (b) Protections for United States facilities or activities.
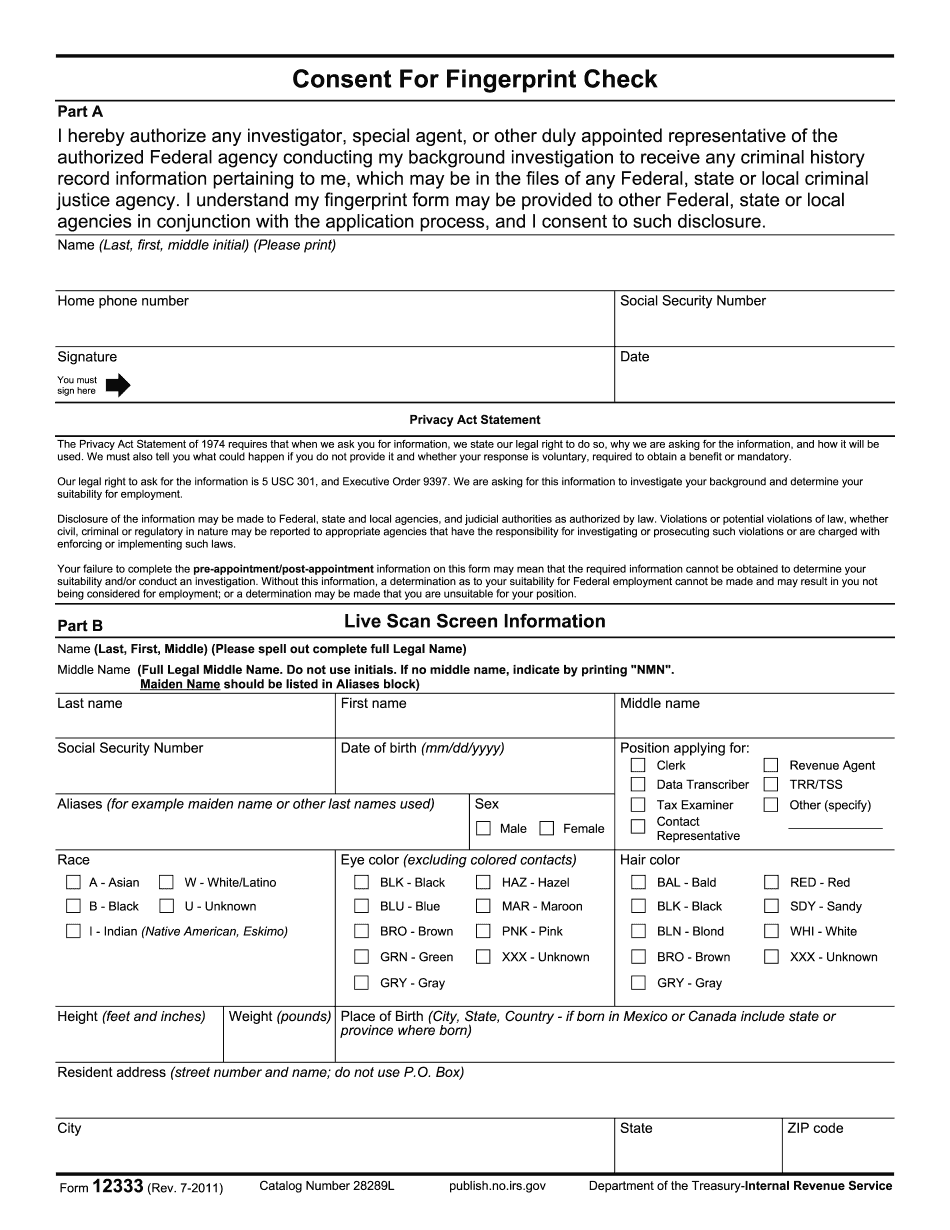
online solutions help you to manage your record administration along with raise the efficiency of the workflows. Stick to the fast guide to do Form 12333, steer clear of blunders along with furnish it in a timely manner:
How to complete any Form 12333 online: - On the site with all the document, click on Begin immediately along with complete for the editor.
- Use your indications to submit established track record areas.
- Add your own info and speak to data.
- Make sure that you enter correct details and numbers throughout suitable areas.
- Very carefully confirm the content of the form as well as grammar along with punctuational.
- Navigate to Support area when you have questions or perhaps handle our assistance team.
- Place an electronic digital unique in your Form 12333 by using Sign Device.
- After the form is fully gone, media Completed.
- Deliver the particular prepared document by way of electronic mail or facsimile, art print it out or perhaps reduce the gadget.
PDF editor permits you to help make changes to your Form 12333 from the internet connected gadget, personalize it based on your requirements, indicator this in electronic format and also disperse differently.
Video instructions and help with filling out and completing Counterintelligence as defined in executive order 12333 as amended is information